In today’s digital age, protecting information is more important than ever. With the rapid growth of online data, understanding data protection and data security in cyber security has become essential worldwide.
Although often used interchangeably, data protection focuses on privacy, legal compliance, and proper data handling, while data security ensures protection against cyber threats and unauthorized access.
This article explains the difference between data security and data privacy, along with practical data protection and data security examples, giving you a clear and complete understanding from a global perspective.
Table of Contents
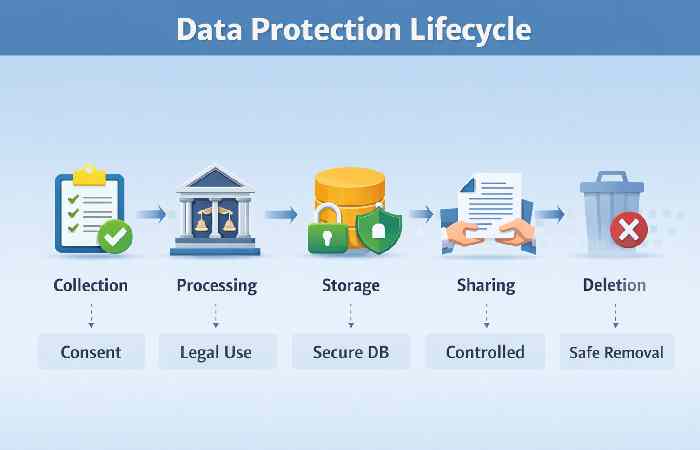
Visual View – Data Protection Lifecycle
Data Protection vs Data Security in Cyber Security (Global Overview)
In modern cyber security frameworks, data protection and data security are interconnected yet fundamentally different disciplines. Globally, organizations rely on both to ensure compliance, trust, and resilience against cyber threats.
Data protection focuses on legal, ethical, and regulatory responsibilities, while data security ensures technical safeguards against breaches, attacks, and unauthorized access.
Core Differences
| Aspect | Data Protection | Data Security |
| Primary Focus | Privacy & legal compliance | Technical defense |
| Objective | Protect personal data rights | Prevent unauthorized access |
| Scope | Policies, laws, governance | Tools, encryption, firewalls |
| Example | GDPR compliance | Antivirus, firewalls |
| Risk Type | Legal penalties | Cyberattacks |
| Users | Governments, organizations | IT teams, cybersecurity experts |
Global Regulations Comparison

| Region | Regulation | Focus |
| Europe | GDPR | Data privacy & rights |
| USA | CCPA | Consumer data control |
| India | DPDP Act | Personal data protection |
| Global | ISO 27001 | Security management |
Key Takeaways
- Data protection ensures legal compliance worldwide
- Data security prevents data breaches and cyber threats
- Both are essential for business continuity
- Organizations must adopt zero-trust security models
Tools and Technologies Used in Data Security
Modern organizations rely on advanced tools to implement data protection and data security examples effectively.
Security Tools
| Tool | Function |
| Firewall | Blocks unauthorized access |
| Encryption | Secures data |
| VPN | Secure communication |
| IDS/IPS | Detects intrusions |
| SIEM | Monitors security events |
Technology Trends
| Technology | Use Case |
| AI Security | Threat detection |
| Blockchain | Data integrity |
| Cloud Security | Remote protection |
| Zero Trust | Strict access control |
Data Protection and Data Security Examples (Real-World Use Cases)
Understanding data protection and data security examples helps organizations implement effective strategies across industries.
Real-World Examples
| Industry | Data Protection Example | Data Security Example |
| Healthcare | Patient consent policies | Encrypted medical records |
| Banking | KYC compliance | Fraud detection systems |
| Education | Student data privacy rules | Secure login systems |
| E-commerce | Privacy policy | Payment encryption |
Threat vs Protection Mapping
| Threat Type | Data Security Measure | Data Protection Measure |
| Phishing | Email filtering | User awareness policies |
| Malware | Antivirus software | Data handling policies |
| Identity Theft | Multi-factor authentication | Privacy laws |
| Data Leak | Encryption | Data minimization |
For global best practices, refer to:
National Institute of Standards and Technology Cybersecurity Framework
https://www.nist.gov/cyberframework
European Union Agency for Cybersecurity Guidelines
https://www.enisa.europa.eu
Types of Data Covered Under Data Protection
Understanding different data types is essential in implementing data protection and data security in cyber security strategies globally.
Types of Data
| Data Type | Description | Example |
| Personal Data | Identifiable information | Name, email |
| Sensitive Data | High-risk personal info | Health records |
| Financial Data | Monetary information | Bank details |
| Organizational Data | Business info | Trade secrets |
| Behavioral Data | User activity | Browsing history |
Key Points
- Sensitive data requires higher protection standards
- Financial data is the top target for cybercriminals
- Global laws strictly regulate personal data usage
Difference Between Data Security and Data Privacy (Deep Analysis)
The difference between data security and data privacy is often misunderstood globally.
- Data privacy defines who can access data
- Data security ensures data is protected from breaches
Privacy vs Security
| Feature | Data Privacy | Data Security |
| Definition | Control over personal data | Protection of data |
| Focus | Rights & consent | Threat prevention |
| Example | Cookie consent | Firewall |
| Goal | Ethical use | Safe storage |
Implementation Layers
| Layer | Data Privacy | Data Security |
| Policy | Privacy policies | Security policies |
| Technology | Consent tools | Encryption tools |
| Governance | Legal compliance | Risk management |
Personal Data Protection of Cyber Information
The protection of personal data is a text in Art. 44.2 of the Makeup of the Dominican Republic, And also which stipulates: “Everyone has the right of access to information and data held about him or his property in official or private records.
As well as knowledge of the destination use with the legally stipulated restrictions. There are also Treatment of personal or property data and information must carry out with due observance. Of the principles of quality, legality, loyalty, security, and practicality. You can ask the competent judicial authority to update, object to the treatment, rectification, or destruction of information that unlawfully affects your rights.
The country has an organic law for the protection of personal data. Law, by the Executive on December 13, 2013, has the primary objective of “the protection of personal data stored in files. Public registers, databases or other technical means of data processing for reporting purposes public or private, as well as that people’s right to honor and privacy.
This new regulation also regulates the establishment, organization, activities, operation, And dissolution of credit reference agencies (SIC), as well as the provision of credit reference agencies and the provision of information in the market, while ensuring respect for the privacy and rights of” the Owner of the information.”
Common Cyber Threats Affecting Data Security
Cyber threats are evolving globally, making data security a critical defense mechanism.
Cyber Threat Landscape
| Threat | Description | Impact |
| Phishing | Fake emails to steal data | Identity theft |
| Ransomware | Locks data for payment | Financial loss |
| Insider Threats | Internal misuse | Data leakage |
| DDoS Attacks | Server overload | Service disruption |
| Malware | Malicious software | Data corruption |
Prevention Techniques
| Threat | Prevention |
| Phishing | Email filtering |
| Malware | Antivirus |
| Ransomware | Backup systems |
| Insider Threat | Access control |
| DDoS | Network monitoring |
Key Principles of Data Protection and Data Security
Globally, both data protection and data security rely on foundational principles that guide organizations in handling sensitive information responsibly and securely.
Core Principles Comparison
| Principle | Data Protection | Data Security |
| Confidentiality | Personal data access control | Encryption & authentication |
| Integrity | Accurate and updated data | Data validation & hashing |
| Availability | Right to access data | Backup & disaster recovery |
| Transparency | Clear data usage policies | Monitoring systems |
| Accountability | Legal responsibility | Security audits |
Global Best Practices
| Practice | Description |
| Data Minimization | Collect only necessary data |
| Encryption | Protect data in transit & storage |
| Access Control | Role-based permissions |
| Regular Audits | Identify vulnerabilities |
| Incident Response | Quick breach handling |
The Social Insurance Fund (TSS) Data Protection and Data Security
And also Has the request of personal data under the mandate of which is based on the comprehensive protection of personal data in files, public records, data bases .Or other technical means of data processing that intend public or private To issue reports. Therefore Citizens who wish to obtain information on their Dominican social security system data should contact the Directorate for Information. And Defense of Affiliated Companies.
Therefore, The Dominican Republic is a signatory to both initiatives and is pursuing the same goal with its information. Security policy in human cyberspace in addition. The state will always protect citizens’ information to prevent identity theft and electronic identity theft.
The state policy states that when an entity in the Dominican state collects personal information. From citizens, the data collected must be protected and never shared or disclosed to private companies. Under any concept or excuse.
It can only guide Dominican public order or improve the personal well-being of each individual. And never attack the dignity or honor of citizens. Now may it use to discriminate in the provision of work, health care. The receipt of social or educational benefits, or democratic participation.
Challenges in Implementing Data Protection Globally
Despite advancements, organizations face multiple challenges in implementing data protection and data security notes worldwide.
Key Challenges
| Challenge | Description |
| Regulatory Differences | Different laws globally |
| Data Volume | Massive data growth |
| Cyber Threats | Increasing attacks |
| Cost | High security investment |
| Awareness | Lack of training |
Solutions
| Challenge | Solution |
| Regulations | Compliance frameworks |
| Data Volume | Cloud storage |
| Threats | AI-based security |
| Cost | Scalable solutions |
| Awareness | Training programs |
Data Protection and Data Security Course & Career Scope
With rising cyber threats, data protection and data security courses are in high demand globally.
Professionals trained in cyber security can work in:
- IT security
- Risk management
- Compliance
- Ethical hacking
Career Opportunities
| Role | Average Salary (Global) | Skills Required |
| Cybersecurity Analyst | $70K–$120K | Network security |
| Data Protection Officer | $80K–$150K | Compliance laws |
| Ethical Hacker | $60K–$130K | Penetration testing |
| Security Engineer | $90K–$160K | Encryption, systems |
Popular Certifications
| Certification | Provider |
| CISSP | (ISC)² |
| CEH | EC-Council |
| CompTIA Security+ | CompTIA |
| ISO 27001 Lead Auditor | ISO |
Future Trends in Data Protection and Data Security
The future of data protection and data security in cyber security is driven by innovation and global collaboration.
Future Trends
| Trend | Impact |
| AI & Automation | Faster threat detection |
| Zero Trust Security | No implicit trust |
| Privacy by Design | Built-in protection |
| Quantum Security | Advanced encryption |
| Cloud Security | Scalable protection |
Key Insights
- AI will dominate cybersecurity operations
- Privacy laws will become stricter globally
- Businesses must adopt proactive security models
Conclusion
Data protection and data security in cyber security are essential pillars of modern digital infrastructure. While data protection ensures compliance with global privacy laws, data security provides the technical foundation to safeguard information.
Organizations worldwide must integrate both strategies to build trust, avoid legal risks, and ensure long-term sustainability in an increasingly digital world.


